10 Genius Password Tips You Need to Know To Stay Safe Online
After I was compromised along with 150 million other users in the Adobe Breach I decided to clean up my password hygiene. Adobe was using an algorithm without salts so by combining the hashes of other users and by looking at the password reminders others set my password was visible to the rest of the world. I was using a very unsecure password at the time. I luckily was not hijacked but many others were.
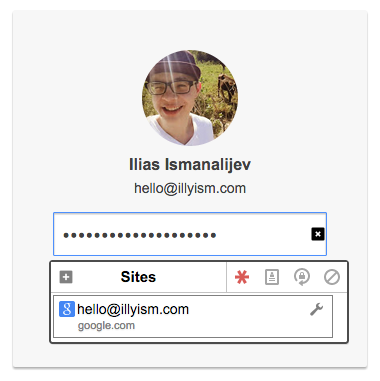
I'm using a password manager right now to authenticate my online services. I'm running it on OS X, Arch Linux, Android and Windows. All the systems that I have are using it right now. I compared password managers and I decided on LastPass because they have good service and try to make it hassle-free to set up. I bought the premium account for some extra features that may not be required for you.
Then I spent a few days changing all the passwords that I ever used and figuring out what I did wrong using the security challenge they provide. Things like duplicate passwords, weak passwords or passwords that may be compromised because of possible data leaks; think Adobe, Sony or LinkedIn.
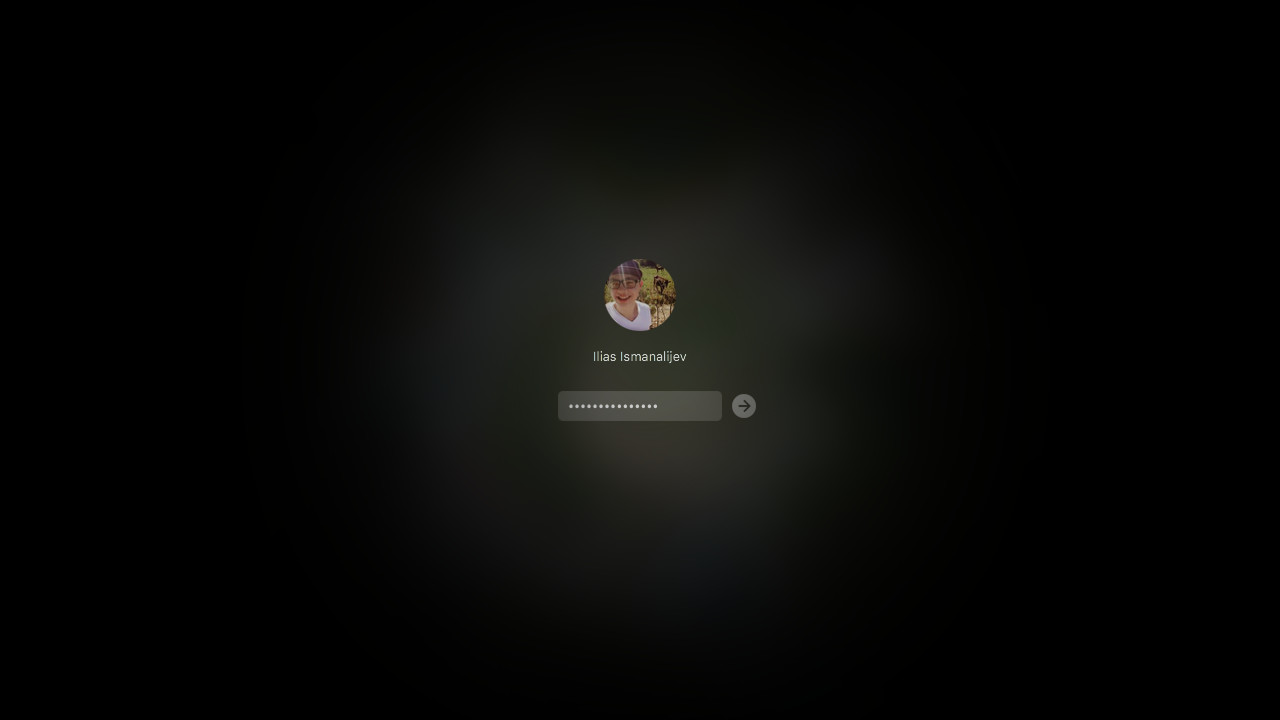
LastPass works out of the box after you install it. It runs offline as a browser extension, I'm using it on Chrome and Firefox. It's easy to get used to as you simply log in using your master password and you then have access to your vault where all your passwords reside.
It works by auto-filling in your browser, then you press submit and you're logged in. It does the same thing on Android devices by detecting password forms and filling it in if it finds a matching service. If you're using another service not in your browser like terminal, a desktop application or perhaps SSH (you should use SSH keys though) you can copy over your password and paste it in those applications.
If you're using someone else's computer you can share your password using the service or copy it over. Then you can change your password right from the extension without having to go to the site.
This service really helps with keeping up your password hygiene. You don't have to worry about remembering your password for every single service that you use and it will keep you from reusing passwords through all the different services or from having a complex password that you would have to write down. The service does it all for you, all your have to do is remember the master password for your vault, which should ideally be secure.
It also has Two-Factor Authentication if you want even more safety through all different kinds of services. This means that if someone compromises your LastPass password they still won't be able to connect if they don't have your phone, which is protected and encrypted. Google Authenticator works the best for me
For example
One of the most important services for me is my Google account so that is locked up separately using Two-Factor Authentication. Nobody can log in without also having your phone. If you happen to wipe your phone and can't use the Authenticator app you're still not completely locked out as you can send a backup code by SMS to your phone number or even use a backup code that you can print out and keep safely somewhere. My Google account has my e-mail that can be used for a password reset and it has my calendar, my google apps domain and whatever else.
A hijacker would have to log in using your generated password which looks something like this:
%Ss0Ay3pVF1^HGfOLF9Jgv18V8rcH@KA0^PvlzB#5ft0q@tj8@a857623A%^SM
This is virtually impossible to determine by brute force given the time that would take is longer than we're alive. Next thing they would need is your phone, so they would need your phone password to be able to access your encrypted phone and pass the 2FA.
Examples of bad passwords
Taken from from the Adobe Breach.
| # | Users | Hash | Password |
|---|---|---|---|
| 1. | 1911938 | EQ7fIpT7i/Q= | 123456 |
| 2. | 446162 | j9p+HwtWWT86aMjgZFLzYg== | 123456789 |
| 3. | 345834 | L8qbAD3jl3jioxG6CatHBw== | password |
| 4. | 211659 | BB4e6X+b2xLioxG6CatHBw== | adobe123 |
| 5. | 201580 | j9p+HwtWWT/ioxG6CatHBw== | 12345678 |
| 6. | 130832 | 5djv7ZCI2ws= | qwerty |
| 7. | 124253 | dQi0asWPYvQ= | 1234567 |
| 8. | 113884 | 7LqYzKVeq8I= | 111111 |
| 9. | 83411 | PMDTbP0LZxu03SwrFUvYGA== | photoshop |
| 10. | 82694 | e6MPXQ5G6a8= | 123123 |
You should check if you have been compromised in the past on https://haveibeenpwned.com/
How easy is it to crack my password?

Keep in mind that the longer your password is the harder it will be to crack. It doesn't matter what order your characters are in but how many characters and the different types of characters it has. Throwing some numbers and special characters in the mix increases the complexity exponentially. A phrase with only letters is usually good enough as long as you don't use it for other websites.
In general:
- numbers only up to 10 characters take 25 seconds to crack.
- words only up to 10 characters take 9 hours to crack.
- words and numbers up to 10 characters take 10 days to crack.
- words, numbers and special characters up to 10 characters take 22 years to crack.
- a phrase with 4 words takes 4 trillion years to crack.
- the random generated password above takes 43 trestrigintillion years (10102) to crack.
- “...no one can hack my mind”: Comparing Expert and Non-Expert Security Practices, July 2015 - https://www.usenix.org/system/files/conference/soups2015/soups15-paper-ion.pdf
- You should check if you have been compromised in the past on https://haveibeenpwned.com/
Ilias is a SEO entrepreneur and marketing agency owner at MagicSpace SEO, helping small businesses grow with SEO. With a decade of experience as a CTO and marketer, he offers SEO consulting and SEO services to clients worldwide.
